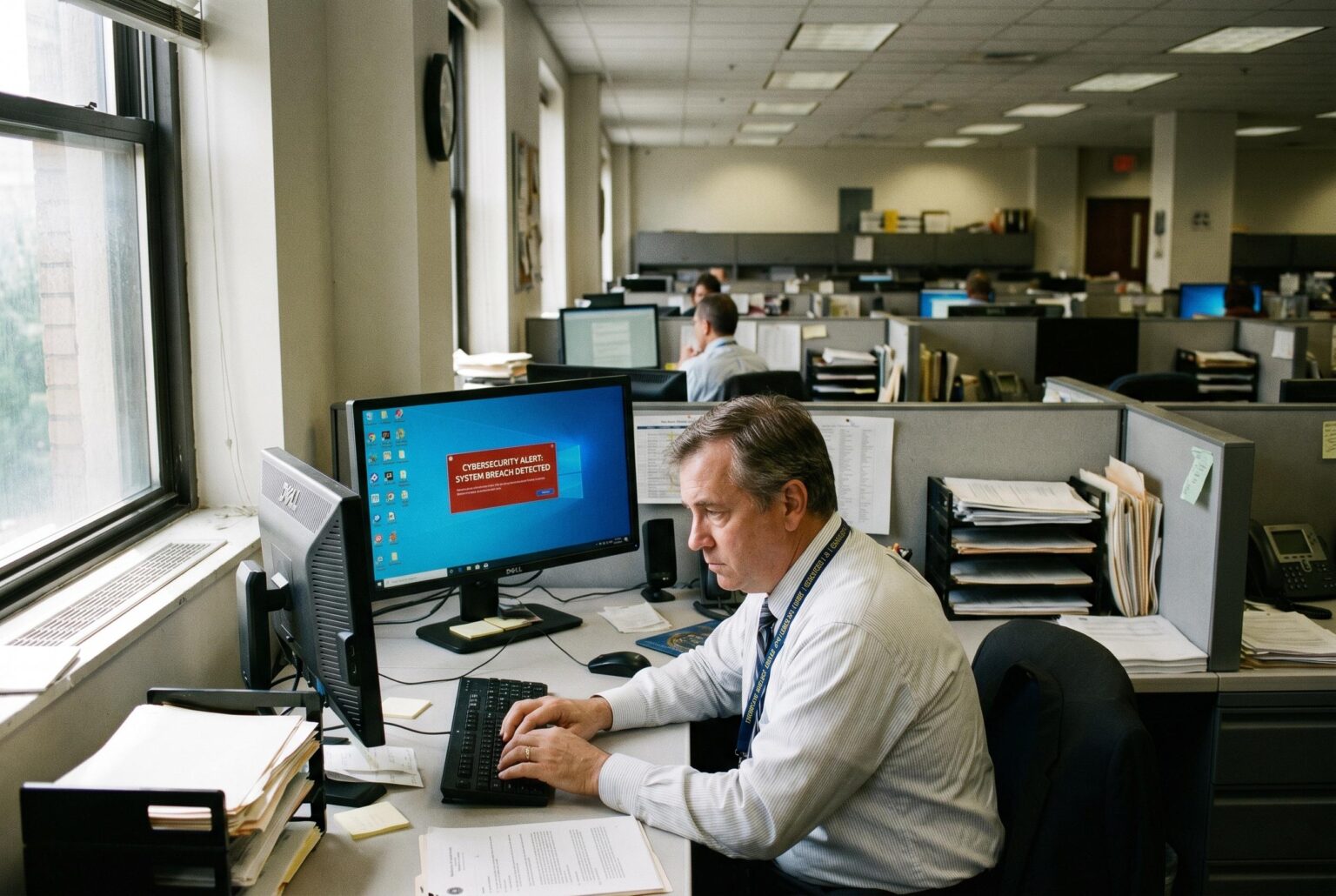
The US Cybersecurity and Infrastructure Security Agency has ordered federal departments to fix a critical Windows flaw, CVE-2026-32202, after it was linked to active zero-day attacks and espionage by Russian hackers, highlighting escalating cyber threat dynamics.
The US Cybersecurity and Infrastructure Security Agency has told federal departments to secure Windows systems after a flaw linked to active zero-day attacks was added to its Known Exploited Vulnerabilities catalogue. The issue, tracked as CVE-2026-32202, has been described by Akamai as a zero-click NTLM hash leak that remained after Microsoft’s February fix for a separate Windows Remote Code Execution bug proved incomplete.
According to CISA, the vulnerability was added to the catalogue on 28 April, with civilian agencies required to address it by 12 May. The agency said organisations should apply vendor mitigations where available, follow binding guidance for cloud services, or stop using the affected product if no workable mitigation exists.
Security researchers say the weakness is tied to an earlier chain of flaws that had already been abused by the Russian espionage group APT28, also known as Fancy Bear and UAC-0001. CERT-UA said that campaign hit targets in Ukraine and EU countries in December 2025 and relied on weaponised LNK files alongside a separate Windows Shell issue, CVE-2026-21513, to reach victims.
Help Net Security reported that the latest flaw can expose NTLMv2 hashes simply by a user browsing a folder, without needing to open the malicious file. That makes the issue especially dangerous in enterprise environments, where stolen authentication material can be used to move laterally through networks and escalate access.
Source Reference Map
Inspired by headline at: [1]
Sources by paragraph:
Source: Noah Wire Services
Noah Fact Check Pro
The draft above was created using the information available at the time the story first
emerged. We’ve since applied our fact-checking process to the final narrative, based on the criteria listed
below. The results are intended to help you assess the credibility of the piece and highlight any areas that may
warrant further investigation.
Freshness check
Score:
7
Notes:
The article was published on April 30, 2026, and reports on events up to April 29, 2026. The earliest known publication date of similar content is April 28, 2026, from BleepingComputer. ([bleepingcomputer.com](https://www.bleepingcomputer.com/news/security/cisa-orders-feds-to-patch-windows-flaw-exploited-in-zero-day-attacks/?utm_source=openai)) The narrative appears to be original, with no evidence of recycling from low-quality sites or clickbait networks. The article is based on a press release from CISA, which typically warrants a high freshness score. No discrepancies in figures, dates, or quotes were found. The article includes updated data and does not recycle older material.
Quotes check
Score:
8
Notes:
The article includes direct quotes from CISA and Akamai. The earliest known usage of these quotes is in the BleepingComputer article published on April 28, 2026. ([bleepingcomputer.com](https://www.bleepingcomputer.com/news/security/cisa-orders-feds-to-patch-windows-flaw-exploited-in-zero-day-attacks/?utm_source=openai)) The wording of the quotes matches across sources, indicating consistency. No online matches were found for other quotes, but this does not necessarily indicate unverifiable content.
Source reliability
Score:
6
Notes:
The article originates from Lifeboat News, a niche publication. While it is reputable within its niche, its reach is limited compared to major news organisations. The article is based on a press release from CISA, which is a primary source. However, the article does not appear to be summarising, rewriting, or aggregating content from another publication.
Plausibility check
Score:
7
Notes:
The article reports on a known vulnerability (CVE-2026-32202) and CISA’s directive to federal agencies, which aligns with information from other reputable sources. The claims are plausible and supported by external reports. The article includes specific factual anchors, such as dates, institutions, and technical details. The language and tone are consistent with typical cybersecurity reporting.
Overall assessment
Verdict (FAIL, OPEN, PASS): PASS
Confidence (LOW, MEDIUM, HIGH): MEDIUM
Summary:
The article is original and reports on a known vulnerability with supporting quotes and references. While the source is a niche publication, the content is plausible and supported by independent verification sources. However, the inclusion of a personal blog as a verification source raises some concerns about source independence.